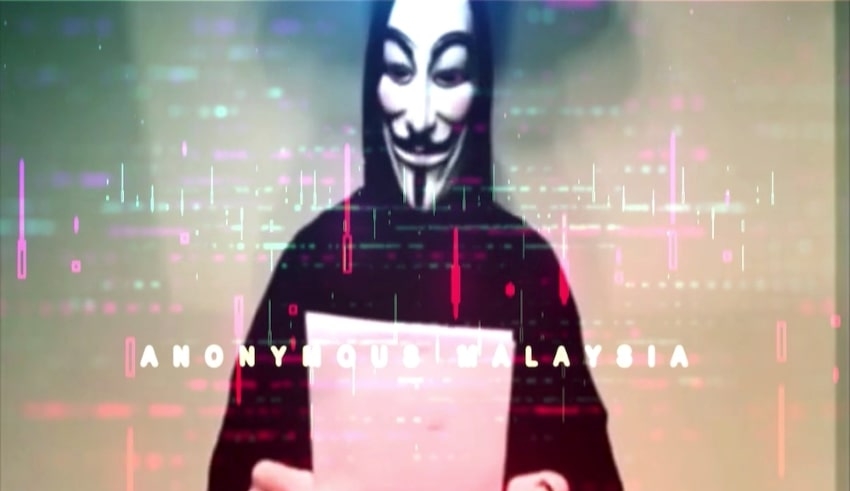
KUALA LUMPUR — As most public and private entities have taken steps to improve the protection of their respective systems and remain vigilant at all times, the risk of cybersecurity threats in the country is still under control. Department chief Megat Muazzam Abdul Mutalib of the Malaysian Computer Emergency Response Team (MyCERT) said the recent threat posed by the hacker activist group Anonymous Malaysia was different from the one identified in 2015.
“There was a clear agenda for the threat in 2015, that is, discontent with the situation at the time and there was an element of (physical) threat. But from what was described in the latest threat, it is more linked to frustration with database problems and data leaks.
“The purposes of these threatening parties include obtaining confidential information, disrupting services or expressing dissatisfaction,” he said when he was contacted by Bernama Radio during today’s Dalam Radar program.
Anonymous Malaysia recently threatened to hack government websites via a video that went viral on social media platforms, alleging that Malaysia’s security system was at a low level, which could allow unscrupulous hackers to easily leak and sell information.
As of yesterday, however, the police said they had not received any complaints of being compromised by government websites.
Meanwhile, through the National Cyber Security Agency (Nacsa), the National Security Council (NSC) has given an alert notice to all government agencies to take the steps required to avoid and mitigate the effect of the cyber threat.
In 2015, the media announced that three individuals alleged to be involved in uploading a YouTube video clip entitled “We Will Blast Malaysia” were detained by the police. The arrest was followed by the release of a one-minute-28-second video clip using the moniker “Anonymous Malaysia,” which revealed a Bangkok, Thailand, bomb blast incident and threatened a similar incident in Malaysia.
Megat Muazzam said there were still a few organizations that were not ready for their cyber threat management strategy, and he hoped that all stakeholders, including organizations, service providers and customers, would be given serious attention to the issue of online threats. The possibility of authorities being able to identify the hackers was high, he said, as each attack typically left a digital trail that could be traced via a logged protection system that could support digital forensic investigations.